As noted in my previous blog, “Incorporating a Sovereign Cloud into a Multicloud Strategy,” high complexity is one of the top 2 challenges organizations face when implementing sovereign cloud solutions (the top challenge is high cost).
Globally, organizations now consider sovereignty to be of great importance. This recognition is at the top level: 86% of CEOs have told us it’s their highest priority in the coming years, ranking alongside the need to address cybersecurity threats (source: IDC’s Worldwide CEO Sentiment Survey [January 2022]; N = 389).
At this stage, it’s worth noting that the aim of sovereignty in the digital context is not all about dominance. The ultimate aim of both sovereign solution providers and their customers is to become stronger competitors on the global digital stage.
Put another way, IDC believes digital sovereignty gives data-driven organizations a license to operate.
So how do you go about implementing sovereign solutions? It begins with customer organizations asking themselves whether they consider digital sovereignty to be a strategic priority.
Of course, the answer could be “no.”
But these organizations should consider if sovereignty is mandated by the need to comply with industry regulations or local data privacy laws. If it is, then organizations will need to begin sovereignty journeys.
But once again, the answer could be “no” — in which case these organizations should ask themselves if sovereignty is needed to gain access to an ecosystem of partners.
Still “no”?
Well, at this point, if sovereignty isn’t even important to the organization’s customers or brand, then it may still be worth considering a solution for the business and technical advantages that sovereignty can bring. More on that later.
But for those who have decided upon implementing a sovereign solution, there are two key initial steps.
First, they need to conduct a review of what will be needed for sovereignty. This should include an assessment of current security and compliance processes, tools, platforms, and skill sets.
Next, organizations will need to classify their data and apps according to sovereign requirements. Not all workloads will need to be migrated to a sovereign cloud; only those deemed to include sensitive data that can be classed as “top secret” or “highly confidential” need to be considered.
Basically, these are the data that will have catastrophic consequences for a business if they’re leaked, shared without authority, or the subject of a security breach.
It may look simple on paper, but this data classification exercise is fraught with complexity, especially for organizations that lack the specialist skills needed for sovereignty. These include, for example, expertise in data management and governance, cybersecurity, and API development. The latter is particularly important: Dedicated APIs will help the organization run a sovereign cloud within regulatory and legal frameworks.
As mentioned in my earlier blog, sovereignty solutions are, by nature, restrictive. Working in an ecosystem that includes partnerships between global and local providers is vital to ensure the balance necessary to maintain sovereignty but not stifle innovation.
The final part of the deployment process is to maintain security and compliance on an ongoing basis. This must be a shared responsibility between all partners. User organizations should largely take responsibility for security in a sovereign cloud; the provider has to account for security of the sovereign cloud.
Suggested Framework for Implementing Sovereign Solutions
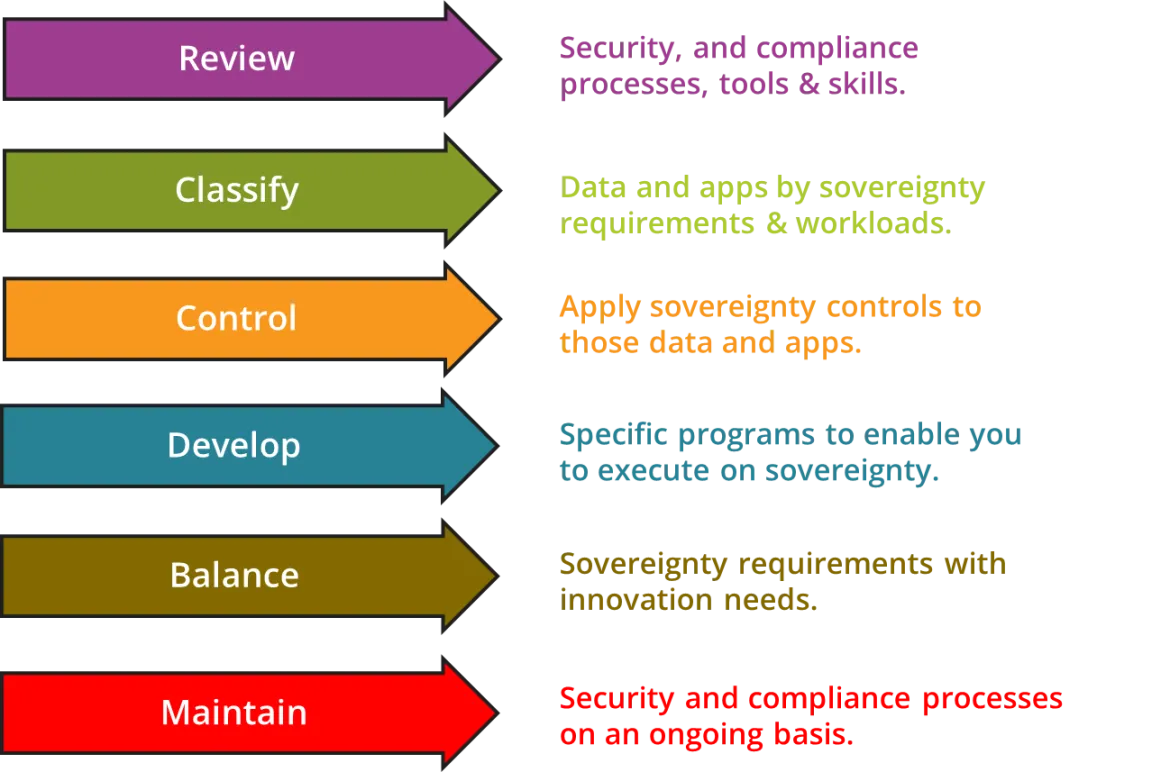
Source: IDC
Despite the challenges of implementing a sovereign solution, there are benefits to be had — even for organizations that do not consider sovereignty to be a must.
IDC research has shown that 71%* of organizations believe that digital sovereignty helps level the playing field and prevents unfair competition in digital markets. Nearly four-fifths (78%)* say it gives them greater control over their data and digital infrastructure and improves their ability to shape digital transformation efforts in a self-determined way.
More than three-quarters* of organizations around the world believe digital sovereignty enhances customer, government, and stakeholder trust in their operations and businesses and can therefore open access to new global markets.
*Source: IDC’s Future Enterprise Resiliency and Spending Survey — Wave 8 (September 2021); N = 800
À propos de l'auteur
Rahiel Nasir is responsible for leading and contributing to IDC's European cloud and cloud data management research programs, as well as supporting associated consulting projects.
In addition, he is the lead analyst for IDC's worldwide Digital Sovereignty research program.
Nasir has been watching technology markets and writing about them throughout his professional life.
Prior to joining IDC, he was a research analyst with 451 Research (now part of S&P Global Market Intelligence), where he covered the datacenter infrastructure and services markets across the EMEA region.
Parcourir par canal
Automatisation
Les dernières nouveautés en matière d'automatisation informatique pour les technologies, les équipes et les environnements
Intelligence artificielle
Actualité sur les plateformes qui permettent aux clients d'exécuter des charges de travail d'IA sur tout type d'environnement
Cloud hybride ouvert
Découvrez comment créer un avenir flexible grâce au cloud hybride
Sécurité
Les dernières actualités sur la façon dont nous réduisons les risques dans tous les environnements et technologies
Edge computing
Actualité sur les plateformes qui simplifient les opérations en périphérie
Infrastructure
Les dernières nouveautés sur la plateforme Linux d'entreprise leader au monde
Applications
À l’intérieur de nos solutions aux défis d’application les plus difficiles
Programmes originaux
Histoires passionnantes de créateurs et de leaders de technologies d'entreprise
Produits
- Red Hat Enterprise Linux
- Red Hat OpenShift
- Red Hat Ansible Automation Platform
- Services cloud
- Voir tous les produits
Outils
- Formation et certification
- Mon compte
- Assistance client
- Ressources développeurs
- Rechercher un partenaire
- Red Hat Ecosystem Catalog
- Calculateur de valeur Red Hat
- Documentation
Essayer, acheter et vendre
Communication
- Contacter le service commercial
- Contactez notre service clientèle
- Contacter le service de formation
- Réseaux sociaux
À propos de Red Hat
Premier éditeur mondial de solutions Open Source pour les entreprises, nous fournissons des technologies Linux, cloud, de conteneurs et Kubernetes. Nous proposons des solutions stables qui aident les entreprises à jongler avec les divers environnements et plateformes, du cœur du datacenter à la périphérie du réseau.
Sélectionner une langue
Red Hat legal and privacy links
- À propos de Red Hat
- Carrières
- Événements
- Bureaux
- Contacter Red Hat
- Lire le blog Red Hat
- Diversité, équité et inclusion
- Cool Stuff Store
- Red Hat Summit

