Following the announcement of the beta of the Red Hat Insights malware detection service in August, we are pleased to announce that this service is now generally available. The malware detection service is a monitoring and assessment tool that scans Red Hat Enterprise Linux (RHEL) systems for the presence of malware, utilizing over 180 signatures of known Linux malware provided in partnership with the IBM X-Force Threat Intelligence team. The Insights analysis provides:
- The list of signatures scanned against your RHEL systems, with links to reference information and analysis reports
- Results for individual system scans and aggregated results for all of your RHEL systems
As part of Insights, malware detection is included in your RHEL subscription. Malware detection supports RHEL 8 and 9 hosts.
Getting started
To scan your RHEL systems for potential malware, please follow our getting started guide. For RHEL 8 and 9 hosts that are already registered to Insights, you will need to install the YARA scanning tool, provided in RHEL 8 and 9 appstream repositories, and run your first scan:
$ sudo dnf install yara $ sudo insights-client --collector malware-detection
When the initial test scan completes successfully, you will be prompted to configure your system for a full scan and set options that control the parameters of that scan, such as which file directories are included or excluded. After your first full scan, you can view the results in Insights malware detection. Subsequent scans will need to be run manually, scheduled using a tool like cron, or automated with a Red Hat Ansible Automation Platform playbook.
Please note: Due to the potentially sensitive nature of this information, only Organizational Admins have default access to the results by default. All other users must first be given access to the service, as detailed in section 2.2. of the Insights malware detection guide.
Interpreting the results
In most cases, scans for potential malware threats on your secure RHEL hosts will result in no matches. In the event that potential malware signature matches are found on your systems, you will see a screen like the one below.
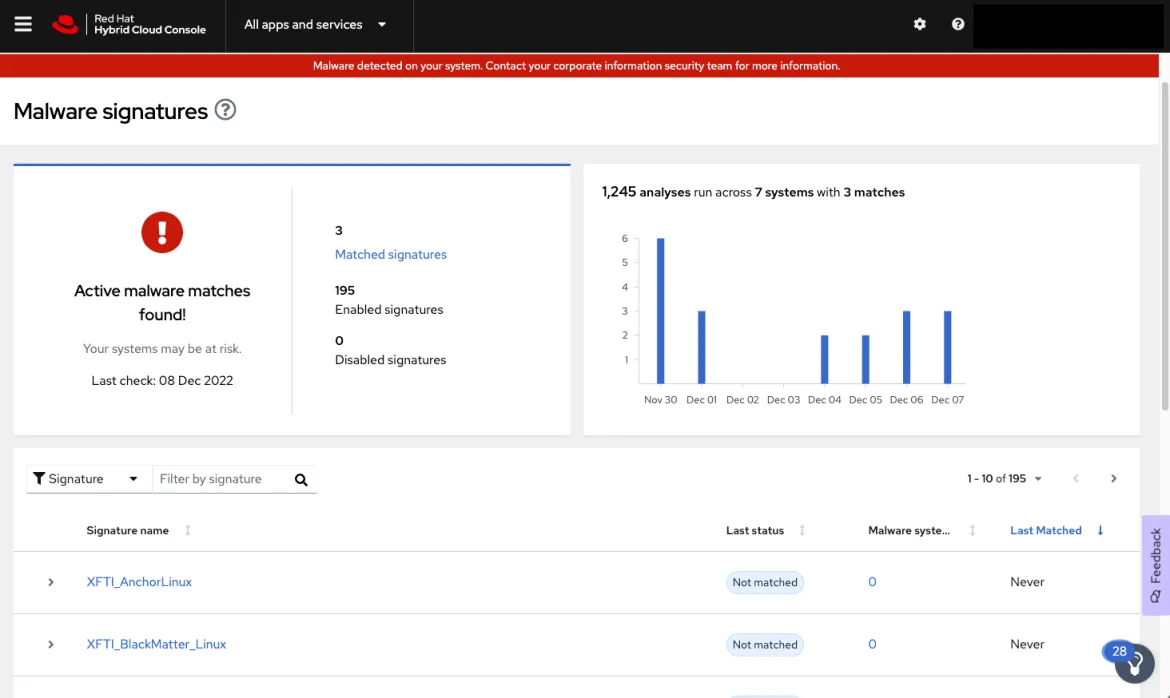
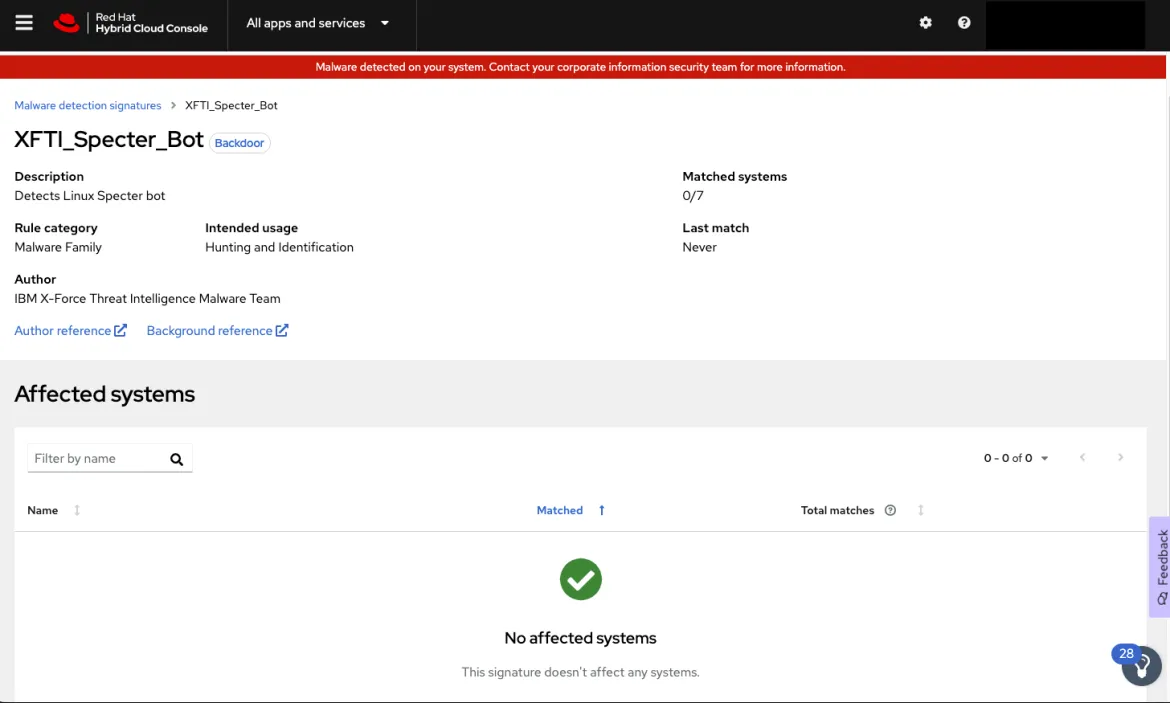
Clicking on a signature name will take you to a page that shows the details about the signature, the number of systems that were matched, and details about when and where the matches were found.
What you do next will depend on the capabilities and needs of your organization. For example, you might have an existing playbook or information security team to consult. If you do not have access to those resources and are uncertain on how to proceed, there are a number of vendors who can provide these services, including the IBM X-Force Incident Response team. Please note: Red Hat does not provide threat response services or consultation.
Additional malware signature information
Each of the over 180 signatures of known Linux malware in Insights malware detection includes additional information, such as the type, category and how it is used. Many of the signatures include links to IBM X-Force analysis reports and additional background information on how the malware was initially identified.
Any feedback about the new malware detection service can be sent to us using the Feedback button inside of Insights—you can see it in the above screenshot on the lower right hand side of the page. Please give the Insights malware detection service a try soon!
À propos de l'auteur
Shane McDowell is a Principal Product Manager for Red Hat. He is focused on helping customers manage their infrastructure in the hybrid cloud. He brings 20+ years of experience with delivering and supporting technology solutions to users in a variety of industries, including Information Technology, Talent Acquisition and Residential Management.
Parcourir par canal
Automatisation
Les dernières nouveautés en matière d'automatisation informatique pour les technologies, les équipes et les environnements
Intelligence artificielle
Actualité sur les plateformes qui permettent aux clients d'exécuter des charges de travail d'IA sur tout type d'environnement
Cloud hybride ouvert
Découvrez comment créer un avenir flexible grâce au cloud hybride
Sécurité
Les dernières actualités sur la façon dont nous réduisons les risques dans tous les environnements et technologies
Edge computing
Actualité sur les plateformes qui simplifient les opérations en périphérie
Infrastructure
Les dernières nouveautés sur la plateforme Linux d'entreprise leader au monde
Applications
À l’intérieur de nos solutions aux défis d’application les plus difficiles
Programmes originaux
Histoires passionnantes de créateurs et de leaders de technologies d'entreprise
Produits
- Red Hat Enterprise Linux
- Red Hat OpenShift
- Red Hat Ansible Automation Platform
- Services cloud
- Voir tous les produits
Outils
- Formation et certification
- Mon compte
- Assistance client
- Ressources développeurs
- Rechercher un partenaire
- Red Hat Ecosystem Catalog
- Calculateur de valeur Red Hat
- Documentation
Essayer, acheter et vendre
Communication
- Contacter le service commercial
- Contactez notre service clientèle
- Contacter le service de formation
- Réseaux sociaux
À propos de Red Hat
Premier éditeur mondial de solutions Open Source pour les entreprises, nous fournissons des technologies Linux, cloud, de conteneurs et Kubernetes. Nous proposons des solutions stables qui aident les entreprises à jongler avec les divers environnements et plateformes, du cœur du datacenter à la périphérie du réseau.
Sélectionner une langue
Red Hat legal and privacy links
- À propos de Red Hat
- Carrières
- Événements
- Bureaux
- Contacter Red Hat
- Lire le blog Red Hat
- Diversité, équité et inclusion
- Cool Stuff Store
- Red Hat Summit

