In today's interconnected digital landscape, Domain Name System (DNS) tracking plays a crucial role in networking and security. DNS resolution is a fundamental process that translates human-readable domain names into IP addresses, enabling communication between devices and servers. Depending on how it is configured and manipulated, it can also be a security vulnerability and a tool for firewalling and blocking access to content. DNS resolution benefits from monitoring and analysis for operations excellence, which can be achieved through innovative technologies like eBPF (extended Berkeley Packet Filter).
This blog post delves into the world of DNS tracking using eBPF tracepoint hooks, exploring how this powerful combination can be used for various purposes, including network monitoring and security enhancement.
Understanding DNS resolution
Before diving into the specifics of eBPF tracepoint hooks, here is a brief recap on how DNS resolution works. In a Kubernetes architecture, DNS is critical in enabling communication between various components and services within the cluster. Kubernetes uses DNS to facilitate service discovery and resolve domain names to the corresponding IP addresses of pods or services. This process involves multiple steps, including querying DNS servers, caching responses, obtaining the IP address to establish a connection, and caching answers for future re-occurrence of the same DNS query.
Utilizing tracepoint hooks for DNS tracking
Tracepoint hooks are predefined points in the Linux kernel where eBPF programs can be attached to capture and analyze specific events. We leveraged tracepoint hooks associated with DNS resolution processes for DNS tracking, specifically the tracepoint/net/net_dev_queue tracepoint. Then, we parse the DNS header to determine if it is a query or a response, attempt to correlate the query or response with a specific DNS transaction, and then record the elapsed time to compute DNS latency. Furthermore, DNS network flows are enriched with DNS-related fields (id, latency, and response codes) to help build graphs with aggregated DNS statistics and filtering on specific fields for display in the Network Observability console.
Potential use cases
DNS tracking with eBPF tracepoint hooks can serve various purposes:
- Network Monitoring: Gain insights into DNS queries and responses, helping network administrators identify unusual patterns, potential bottlenecks, or performance issues.
- Security Analysis: Detect suspicious DNS activities, such as domain name generation algorithms (DGA) used by malware, or identify unauthorized DNS resolutions that might indicate a security breach.
- Troubleshooting: Debug DNS-related issues by tracing DNS resolution steps, tracking latency, and identifying misconfigurations.
How to enable DNS tracking
By default, DNS tracking is disabled because it requires privileged access. To enable this feature, create a flow collector object with the following fields enabled in the eBPF config section as shown below:
apiVersion: flows.netobserv.io/v1beta1
kind: FlowCollector
metadata:
name: cluster
spec:
agent:
type: EBPF
ebpf:
privileged: true
features:
- DNSTracking
A quick tour of the UI
Once the DNSTracking feature is enabled, the Console plugin will automatically adapt to provide additional filters and show information across views.
Open your OCP Console and move to Administrator view -> Observe -> Network Traffic page as usual.
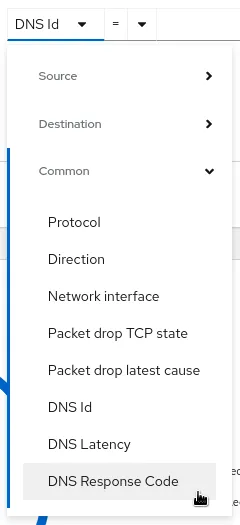
Three new filters, DNS Id, DNS Latency, and DNS Response Code, will be available in the common section:
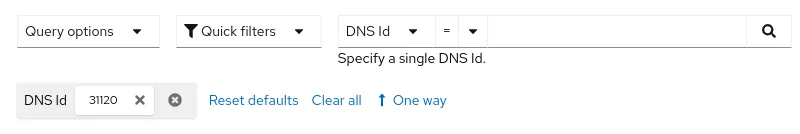
The first option allows you to filter on a specific DNS Id (found using the dig command or flow table details) to correlate with your query:
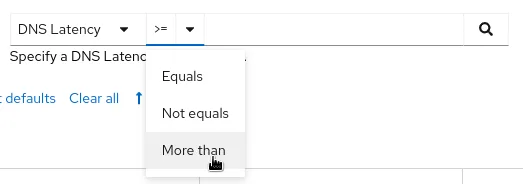
The second choice helps identify potential performance issues by looking at DNS resolution latency:
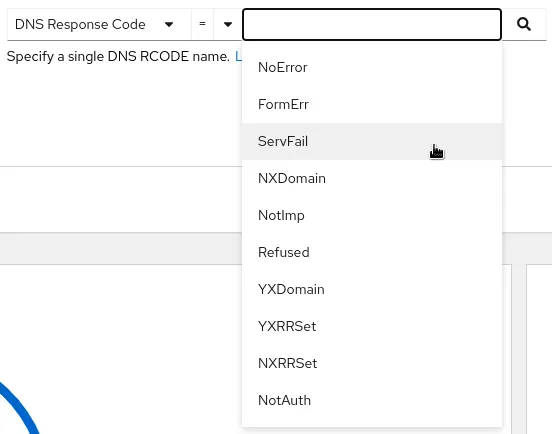
The third filter surfaces DNS response codes, which can help detect errors or unauthorized resolutions:
Overview
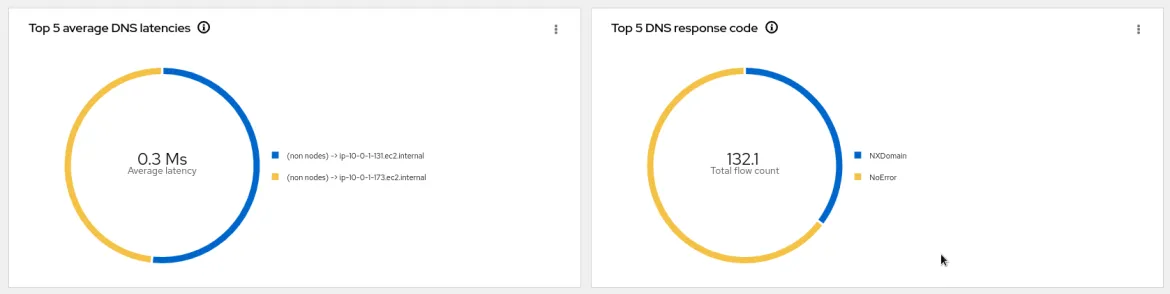
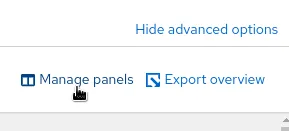
New graphs are introduced in the advanced options -> Manage panels popup:
- Top X average DNS latencies
- Top X DNS response code
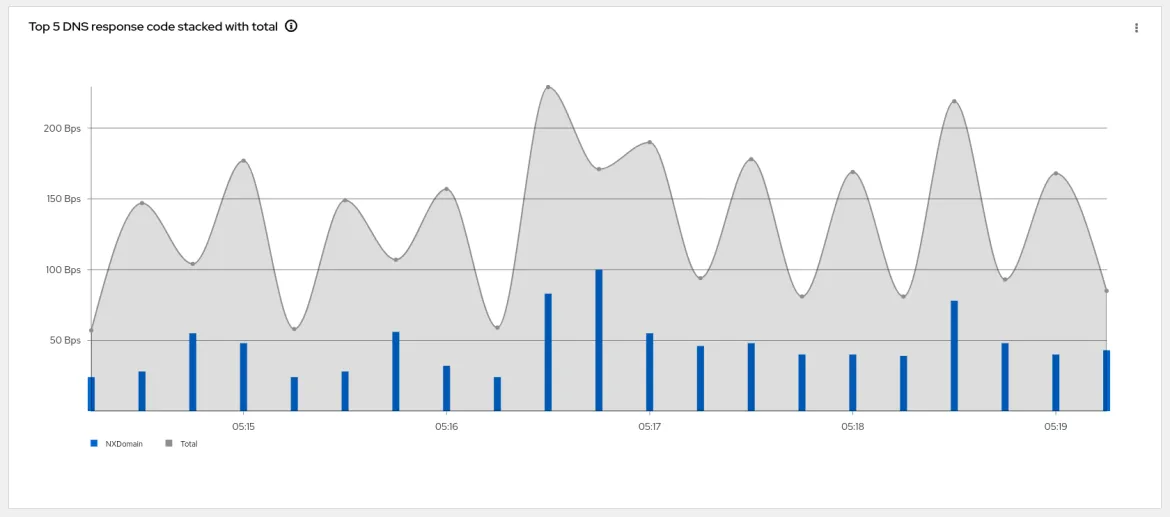
- Top X DNS response code stacked with total
Traffic flows
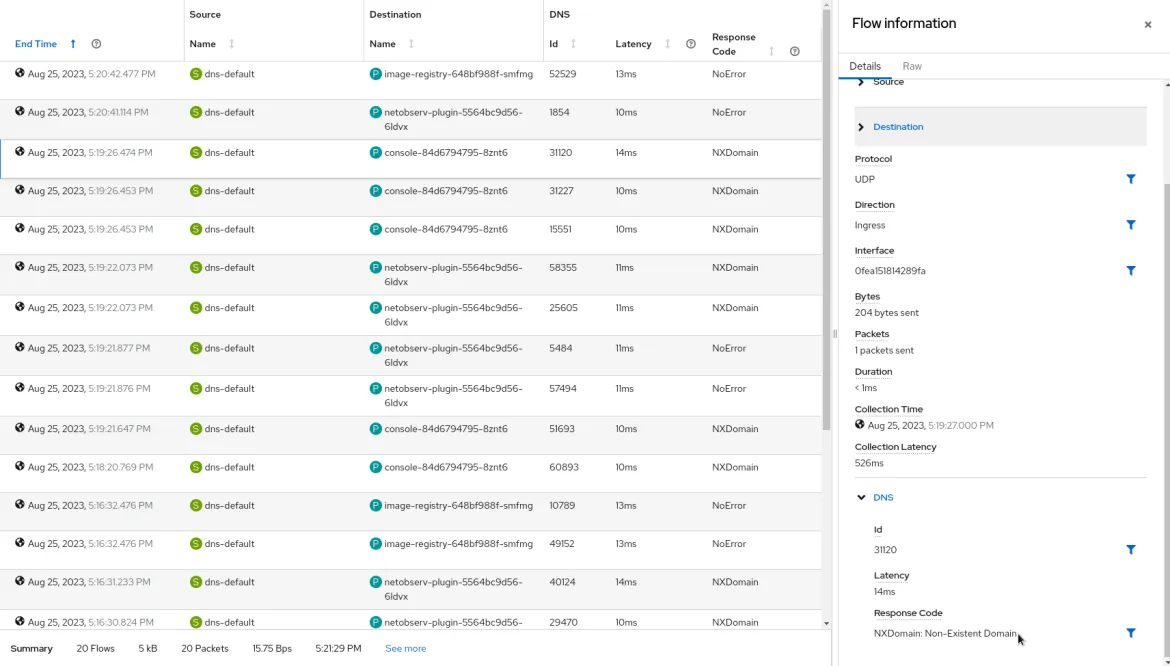
The table view adds the new DNS columns Id, Latency, and Response code, which are available from the advanced options -> manage columns popup:
The DNS flows display this information in both the table and the side panel:
Future support plans
- Adding tracking capability for mDNS.
- Adding support for DNS over TCP.
- Investigating options to handle DNS over TLS where the DNS header is fully encrypted.
Feedback
We hope you liked this article!
Netobserv is an open source project available on GitHub. Feel free to share your ideas, use cases, or ask the community for help.
저자 소개
채널별 검색
오토메이션
기술, 팀, 인프라를 위한 IT 자동화 최신 동향
인공지능
고객이 어디서나 AI 워크로드를 실행할 수 있도록 지원하는 플랫폼 업데이트
오픈 하이브리드 클라우드
하이브리드 클라우드로 더욱 유연한 미래를 구축하는 방법을 알아보세요
보안
환경과 기술 전반에 걸쳐 리스크를 감소하는 방법에 대한 최신 정보
엣지 컴퓨팅
엣지에서의 운영을 단순화하는 플랫폼 업데이트
인프라
세계적으로 인정받은 기업용 Linux 플랫폼에 대한 최신 정보
애플리케이션
복잡한 애플리케이션에 대한 솔루션 더 보기
오리지널 쇼
엔터프라이즈 기술 분야의 제작자와 리더가 전하는 흥미로운 스토리
제품
- Red Hat Enterprise Linux
- Red Hat OpenShift Enterprise
- Red Hat Ansible Automation Platform
- 클라우드 서비스
- 모든 제품 보기
툴
체험, 구매 & 영업
커뮤니케이션
Red Hat 소개
Red Hat은 Linux, 클라우드, 컨테이너, 쿠버네티스 등을 포함한 글로벌 엔터프라이즈 오픈소스 솔루션 공급업체입니다. Red Hat은 코어 데이터센터에서 네트워크 엣지에 이르기까지 다양한 플랫폼과 환경에서 기업의 업무 편의성을 높여 주는 강화된 기능의 솔루션을 제공합니다.