As your business modernizes its cloud technology, it’s important to scale your cloud environments securely. Azure Red Hat OpenShift (ARO) supports your security needs at scale. With shared responsibility between Red Hat and Microsoft, ARO can help your organization boost cloud security in several ways.
Through ARO’s built-in security features your organization can simplify software deployment and reduce operational complexity with automated security maintenance and ongoing monitoring. The Red Hat Site Reliability Engineering (SRE) team automates, manages and monitors your platform so your business can focus on value-driven tasks without the burden of manually applying security updates and patches. As our SRE teams would say, “We make infrastructure boring.”
We continuously look for ways to improve security standards for customers, and recently we implemented several new security features.
Cybersecurity vulnerabilities (CVEs) and upgrades
Customers are able to take advantage of the benefits of the work the Red Hat Security team provides. The Red Hat security team looks at CVEs, identifies the severity, and if appropriate, provides errata for them. Red Hat Errata helps users determine what updates are available and how important they are based on analysis by Red Hat engineering. A majority of these Erratas will be provided via a version upgrade which can be applied to the clusters through either automated or manual tooling provided as part of Azure Red Hat OpenShift. The automated method leverages the recently released Managed Upgrade Operator. To configure the operator, all you have to do is apply a YAML file with a scheduled time at which you’d like the upgrade to take place and the operator will do the rest. For more details around how to configure the operator, refer to this document.
Cluster configuration upgrades
We continually work with Microsoft and customer security teams on implementing security best practices.
Two recently released features based on customer and Microsoft feedback include Storage and Egress Lockdown.
Storage Lockdown adds increased security to the storage accounts. This was done by changing the configuration of the storage account to force the use of a higher TLS version and a newer storage account version. It also checks to make sure the storage account is private and encryption is turned on. This feature is available for all Azure Red Hat OpenShift customers. Learn more about Storage lockdown.
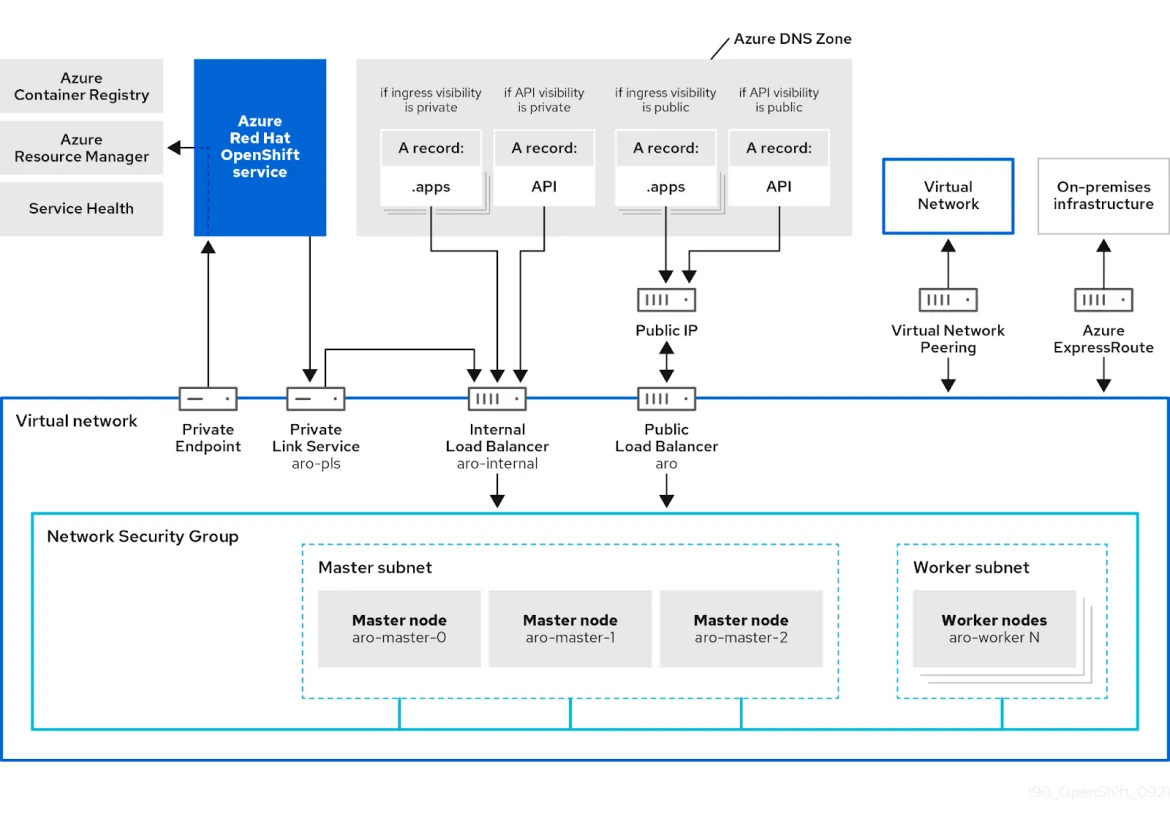
We also received feedback that while private clusters were private (no ingress allowed), customers wanted to limit the remaining dependency on Egress traffic. This dependency’s primary purpose was for the cluster to communicate with Azure endpoints (for example to the Azure container registry). To enhance the security of these deployments, we created a private endpoint which would provide access to the Azure resources, so clusters can be deployed without a path to the Internet, for minimal deployment scenarios. You will notice in the diagram below [1] a private endpoint which provides the cluster access to the service. This private endpoint provides exclusive access to the specific resources that the cluster depends on.
Figure 1 - Network topology of Azure Red Hat OpenShift
Some customers may elect to connect to additional registries or other external resources; this may be recommended for some use cases, as these can provide access to additional Red Hat Operators but this traffic would flow through the VNet peering and Azure Express route. Learn more about Egress Lockdown.
Compliance and certifications
Microsoft Azure offers a range of compliance solutions, and by using Azure Red Hat Openshift, customers get the benefits of Azure’s compliances coupled with Red Hats, combined to provide a large range of options.. Through the collaboration with Microsoft Azure, we have obtained numerous certifications inside their cloud, including PCI DSS, FedRAMP, HIPAA and many more. Visit the Azure compliance page for more information on these.
Red Hat also provides a full set of compliance tooling for additional security needs. Red Hat Advanced cluster Management provides management and controls via built-in policies which can be enforced upon Azure Red Hat OpenShift clusters. Red Hat Advanced Cluster Security (ACS) for Kubernetes provides a native Kubernetes security approach, adding an additional native layer of security to applications on the platform..
If you are looking to get started with Azure Red Hat OpenShift, read this blog to learn how to deploy the product through the Azure portal.
Sobre el autor
Navegar por canal
Automatización
Las últimas novedades en la automatización de la TI para los equipos, la tecnología y los entornos
Inteligencia artificial
Descubra las actualizaciones en las plataformas que permiten a los clientes ejecutar cargas de trabajo de inteligecia artificial en cualquier lugar
Nube híbrida abierta
Vea como construimos un futuro flexible con la nube híbrida
Seguridad
Vea las últimas novedades sobre cómo reducimos los riesgos en entornos y tecnologías
Edge computing
Conozca las actualizaciones en las plataformas que simplifican las operaciones en el edge
Infraestructura
Vea las últimas novedades sobre la plataforma Linux empresarial líder en el mundo
Aplicaciones
Conozca nuestras soluciones para abordar los desafíos más complejos de las aplicaciones
Programas originales
Vea historias divertidas de creadores y líderes en tecnología empresarial
Productos
- Red Hat Enterprise Linux
- Red Hat OpenShift
- Red Hat Ansible Automation Platform
- Servicios de nube
- Ver todos los productos
Herramientas
- Training y Certificación
- Mi cuenta
- Soporte al cliente
- Recursos para desarrolladores
- Busque un partner
- Red Hat Ecosystem Catalog
- Calculador de valor Red Hat
- Documentación
Realice pruebas, compras y ventas
Comunicarse
- Comuníquese con la oficina de ventas
- Comuníquese con el servicio al cliente
- Comuníquese con Red Hat Training
- Redes sociales
Acerca de Red Hat
Somos el proveedor líder a nivel mundial de soluciones empresariales de código abierto, incluyendo Linux, cloud, contenedores y Kubernetes. Ofrecemos soluciones reforzadas, las cuales permiten que las empresas trabajen en distintas plataformas y entornos con facilidad, desde el centro de datos principal hasta el extremo de la red.
Seleccionar idioma
Red Hat legal and privacy links
- Acerca de Red Hat
- Oportunidades de empleo
- Eventos
- Sedes
- Póngase en contacto con Red Hat
- Blog de Red Hat
- Diversidad, igualdad e inclusión
- Cool Stuff Store
- Red Hat Summit